What Are Micro Front-ends?
Micro Front-ends decompose a frontend into smaller, independent pieces—each owned by one team, potentially using different tech stacks, and deployed separately. This guide covers implementing Module Federation in Angular with Azure Entra ID and APIM integration.
Introduction
Modern enterprise applications demand scalability, team autonomy, and independent deployability. Micro Front-ends address these needs by applying microservices principles to frontend development. Instead of a monolithic frontend, you build smaller, loosely coupled applications that compose into a unified user experience.
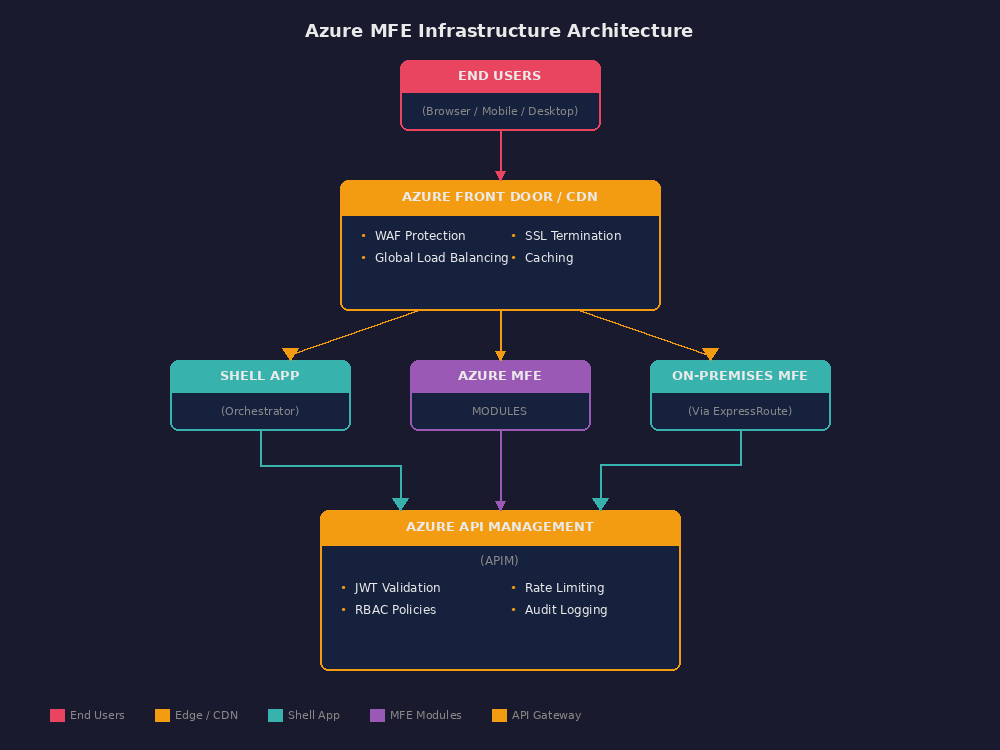
This series guides you through implementing Micro Front-ends using Webpack Module Federation in Angular, integrated with Azure Entra ID for authentication and Azure API Management (APIM) for API governance. You'll learn the architectural patterns, security considerations, and operational practices that make this approach successful.
Micro Front-ends extend the microservices philosophy to the browser. Each micro frontend (MFE) represents a distinct business capability, owned end-to-end by a single team. Teams can choose their technology stack, deploy on their own schedule, and evolve their codebase independently.
Core Characteristics
| Characteristic | Description |
|---|---|
| Independent Deployability | Each MFE deploys without coordinating with other teams |
| Team Ownership | One team owns the entire vertical slice—UI to backend |
| Technology Agnostic | Teams can use different frameworks (with governance) |
| Isolated Failure | One MFE's failure doesn't cascade to others |
| Shared Nothing | Minimal shared state between MFEs |
Key Architecture Decisions
When designing your Micro Frontend architecture, you'll face several foundational choices. Here are the decisions that shape this reference architecture:
| Decision | Rationale | Impact |
|---|---|---|
| Module Federation over iframes | Better performance, shared dependencies, native Angular integration | Requires version alignment strategy |
| Shell as single auth authority | Centralized token management, consistent security posture | Shell becomes critical path |
| APIM for all backend calls | Unified policy enforcement, audit logging, rate limiting | Additional network hop |
| Dynamic remote loading | Enables independent deployments, graceful degradation | Requires robust error handling |
| Hybrid deployment model | Supports cloud-first with on-premises integration | Complex network architecture |
Success Criteria
Before diving into implementation, establish measurable success criteria:
- Independent deployment capability for each micro frontend within 30 minutes
- Zero authentication failures during MFE transitions
- Sub-second module loading for cached resources
- 99.9% availability for the shell application
- Complete audit trail for all API calls through APIM
What This Series Covers
This comprehensive guide walks through every aspect of building production-ready Micro Front-ends:
| Topic Area | What You'll Learn |
|---|---|
| Module Federation | Host/remote configuration, shared dependencies, dynamic loading |
| Security | JWT federation, Azure Entra ID integration, defense-in-depth |
| API Gateway | APIM policies, rate limiting, request transformation |
| Networking | Hybrid connectivity, NSGs, CORS configuration |
| Team Organization | Ownership models, development standards, communication patterns |
| Governance | Architecture review, change management, compliance |
| DevOps | CI/CD pipelines, deployment strategies, IaC |
| Observability | Monitoring, distributed tracing, alerting |
| Disaster Recovery | Failover architecture, recovery objectives |
Key Takeaways
-
Micro Front-ends decompose frontend monoliths — Each team owns a vertical slice from UI to backend, enabling independent development and deployment.
-
Module Federation enables runtime composition — Webpack's Module Federation allows loading separately-built applications at runtime with shared dependencies.
-
Security requires defense-in-depth — JWT federation, APIM policies, and Zero Trust principles protect the distributed architecture.
-
Success demands clear governance — Version compatibility, communication contracts, and review processes keep teams aligned.

